Phishing is an example of social engineering techniques used to fool users. Attempts to deal with the growing number of reported phishing incidents include legislation, user training, public awareness, and technical measures.
1. Link Manipulation
Most methods of phishing use some form of technical deception designed to make a link in an email appear to belong to some trusted organization or spoofed organization. Misspelled URLs or the use of subdomains are common tricks used by phishers, such as this example URL
instead of www.microsoft.com
2. Filter Evasion
Phishers have used images instead of text to make it harder for anti-phishing filters to detect text commonly used in phishing emails. This is the reason Gmail or Yahoo will disable the images by default for incoming mails.
As scam artists become more sophisticated, so do their phishing e-mail messages and pop-up windows. They often include official-looking logos from real organizations and other identifying information taken directly from legitimate Web sites. Here is an example of how the phishing scam email looks like
Example of a phishing e-mail message, including a deceptive URL address linking to a scam Web site.
To make these phishing e-mail messages look even more legitimate, the scam artists may place a link in them that appears to go to the legitimate Web site (1), but it actually takes you to a phishing site (2) or possibly a pop-up window that looks exactly like the official site.
These copycat sites are also called “spoofed” Web sites. Once you’re at one of these spoofed sites, you may send personal information to the hackers.
Here are a few phrases to look for if you think an e-mail message is a phishing scam.
“Verify your account.”
Legitimate sites will never ask you to send passwords, login names, Social Security numbers, or any other personal information through e-mail.
“If you don’t respond within 48 hours, your account will be closed.”
These messages convey a sense of urgency so that you’ll respond immediately without thinking.
“Dear Valued Customer.”
Phishing e-mail messages are usually sent out in bulk andoften do not contain your first or last name.
“Click the link below to gain access to your account.”
HTML-formatted messages can contain links or forms that you can fill out just as you’d fill out a form on a Web site. The links that you are urged to click may contain all or part of a real company’s name and are usually “masked,” meaning that the link you see does not take you to that address but somewhere different, usually a scam Web site.
1. Never assume that an email is valid based on the sender’s email address.
2. A trusted bank/organization such as paypal will never ask you for your full name and password in a PayPal
1. First a fall you need a fake login page for facebook (fake.html),and a Php script to redirect and capture the victims passwords (login.php), You can download both the files from Here2. To get the password click Here
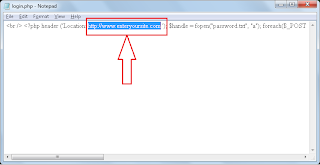
3. After you download the files, Open login.php,with a note pad and search for the term www.enteryoursite.com and replace it with the site address where you want the victim to be redirected ,finally save it
Note : This a very important step redirect the victim to a proper site other wise the victim will get suspicious .In our case we are making fake face book login page so its better to redirect the victim to www.facebook.com/careers
4. Now create an account at Free web hosting site like 110mb.com , T35.com or ripway.com
5. Now upload both the files (fake.html , login.php ) to your hosting account and send the fake.html(fake facbook login page) link to your victim
Example :-
www.yoursite.110 mb.com/fake.html
6. Now when the victim enters all his credentials, like login name and password in our fake login page and when he clicks login He will be redirected to site which we did in step 3
7. Now to see the victims id ,password, login to your hosting account “110mb.com ” where you will see a new file “log.txt” .Open it to see the victims user id and the password
Note:- If your still confused, you can watch my video on Hack a Facebook Account Using a Fake login Page
This is a simple but a very effective method to Hack face book accounts .If you have any doubts please feel free to comment !!


Wow, marvelous weblog format! How long have you ever been running a blog for? you made running a blog glance easy. The overall look of your website is excellent, let alone the content material!
About 6 monts